Massive Text Message Leak Shows 2FA Isn't Safe Either


Over the past few years, scores of data breaches of big companies like Facebook and Yahoo accept made us wary of the tendency of online databases to be vulnerable. But virtually often, nosotros imagine repercussions in the terminology of passwords and the data we enter online, with SMSes hands escaping the inventory of potential culprits.
A recent investigation by TechCrunch has led the states to contemplate the ease with which SMSes can be exploited to hijack different accounts. The server of Voxox, a cloud communications company which offers SMS services enterprises – amid other operations, could exist accessed without a password. The database is at present offline, but the harm could already have been done. Voxox says it's currently evaluating the impact.
This lack of security gave hijackers an easy pass into the "a near-real-time stream of text messages", it was reported. This vulnerability was discovered by a High german bug compensation hunter, Sébastien Kaul. This database was available via Shodan, a public platform for databases intended for wider reach and not usually controlled past corporations.
Kaul easily got access to 26 meg text messages, with neatly stacked metadata which fabricated it piece of cake to squeeze out information like names, real-time erstwhile passwords, internet banking codes, and fifty-fifty two-factor authentication keys.
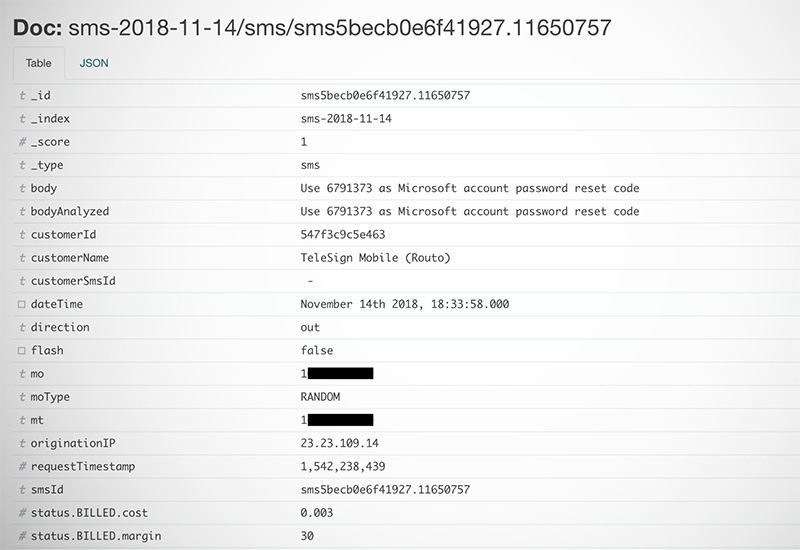
The sheer variety of data that is up for grabs publicly is an eye-opener. Here are the services that TechCrunch has noted could be exploited in instance the database is breached:
- First-fourth dimension verification codes for services such as Viber messenger, online quiz app HQ Trivia, some medical facilities
- 2FA codes and access codes for accessing accounts related to Google, Yahoo, Booking.com, Fidelity Investments
- Countersign reset links and codes for Microsoft and Huawei accounts
- Aircraft notification from Amazon forth with a link for tracking without any credentials
- And even, unencrypted and unprotected passwords for LA-based dating app Badoo
Another security researcher, Dylan Katz who reviewed these findings, also cautioned about "the potential that this has already been abused". If it has, its reach could accept a catastrophic touch on the users whose information was reportedly leaked.
Employ Google Authenticator Not SMS for 2FA
While the impact of this leak is not currently measurable, we recommend you to use Google Authenticator app (free) which generates short–lives numeric codes for the purpose of 2-Factor Hallmark. Although, it must exist noted that Authentication runs on a device and the data is not stored on the deject. While that ensures more than security, you might exist locked out if you lose your smartphone or have it stolen.
Source: https://beebom.com/leak-26-million-text-messages-2fa/
Posted by: whiteheadprifecon.blogspot.com


0 Response to "Massive Text Message Leak Shows 2FA Isn't Safe Either"
Post a Comment